What is NXDOMAIN? How does nxdomain affects my browsing? Explains the relationship between NXDOMAIN and DNS Hijacking.
A DNS server is used to translate a domain name into an IP address or vise versa. For example, when you type dnsknowledge.com in your web browser, an authoritative dns server translate a domain name such as dnsknowledge.com into an IP address such as 67.228.49.226. However, if you try dnsknowledgefoobarexamplefackdomain.com, you will get an error indicating non existing domain name.
Non-existent Internet Domain Names Definition
NXDOMAIN is nothing but non-existent Internet or Intranet domain name. If domain name is unable to resolved using the DNS, a condition called the NXDOMAIN occurred. In this example, try to find out an ip address for the domain called abcquq12examfooltest.com using the nslookup or host command line option:
nslookup abcquq12examfooltest.com
OR
host abcquq12examfooltest.com
Sample outputs:
Host abcquq12examfooltest.com not found: 3(NXDOMAIN)
Since domain name is the invalid domain, you got a NXDOMAIN response i.e an error message indicating that domain is either not registered or invalid.
DNS Hijacking And NXDOMAIN
A few ISPs such as Optimum Online, Comcast, Time Warner, Cox Communications, RCN, Rogers, Charter Communications, Verizon, Virgin Media, Frontier Communications, Bell Sympatico, Airtel, and many others started the bad practice of DNS hijacking on non-existent domain name for making money by displaying the internet advertisements. These ISP and/or advertiser may collect your personal data too. These ISPs DNS server sends a fake IP address for all the NXDOMAIN responses. In most cases your browser will connect to a fake IP address server which will display page with advertising, instead of a proper error message to you. In some cases it is possible to obtain sensitive information too.
When you search for a Web site (domain) that doesn’t exist, these ISPs will hijack your session (also called as Error Redirection service), and it will show suggestions for sites that are similar to what you entered with tons of advertisements. In most circumstances DNS Error Redirection cause problems for customers running various specialty programs (such as game servers) or services (such as corporate vpn client and servers).
Example: DNS Hijacking On Non-existent Domain Name (NXDOMAIN)
The domain name foobar.dnsknowledge.com or a web site http://foobar.dnsknowledge.com doesn’t exist. If you run query for such address most ISPs will hijack your session and display advertisements. A typical dns query will look like as follows using the nslookup command on MS-Windows or host command on Mac OS X/Unix/Linux computer:
nslookup foobar.dnsknowledge.com
OR
host foobar.dnsknowledge.com
Sample outputs:
foobar.dnsknowledge.com has address 92.242.132.8
As a result of this hijacking you will see the following page:
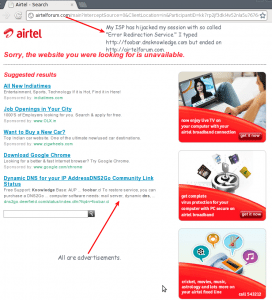
My ISP Has Hijacked Nxdomain Page
Example: Non-existent Domain Name (NXDOMAIN) Response
In this example, I’m using our corporate resolving DNS name servers i.e. I’m not using ISP’s dns server. This ensures that my DNS session can not be hijacked. A typical dns query will look like as follows using the nslookup command on MS-Windows or host command on Mac OS X/Unix/Linux computer:
nslookup foobar.dnsknowledge.com
OR
host foobar.dnsknowledge.com
Sample outputs:
Host foobar.dnsknowledge.com not found: 3(NXDOMAIN)
No ip address returned and I got clean error message. This suggest that the domain foobar.dnsknowledge.com doesn’t exists. I’ve disabled hijacking of NXDOMAIN responses using my own resolving caching dns server:
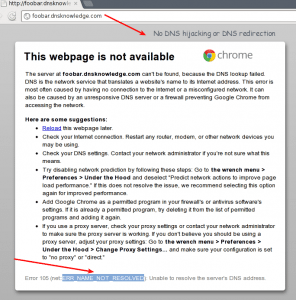
Fig.02: No DNS hijacking / DNS Redirection Example
Summary
- NXDOMAIN error message means that a domain does not exist.
- Some ISPs started DNS hijacking or DNS redirection for NXDOMAIN error messages.
- It is the practice of redirecting the resolution of Domain Name System (DNS) names to other DNS servers or web servers.
- Commonly used for displaying advertisements or collecting statistics.
- This practice violates the RFC standard for DNS (NXDOMAIN) responses.
- Phishing : Cross-site scripting attacks can occurred due to malicious hijacking.
- Censorship : DNS service providers to block access to selected domains.
thanks for contributing.
Thank you for putting an understandable explanation here. I really appreciate it!
Could you please explain the DNS Hijacking part a bit better? Also there are some grammer error which makes it harder to understand. Thanks!
@nottinhill: it’s GRAMMAR
fail.
nottinhill / police:
Thanks for the heads up. The article has been updated.
great article
Somebody knows how to prevent NXDOMAIN to be hijacked by our ISP’s?
You can switch your DNS settings and use a third-party provider. They are usually faster and may have more features (such as filtering & phishing protection). Two examples are Google’s Public DNS and OpenDNS. Both are free. Note that OpenDNS has recently switched from hijacking NXDOMAIN and stopped redirecting NXDOMAIN errors and Google has never been doing it. However, OpenDNS is not entirely RFC compliant, as they explain below:
“However, we still intercept phishing and malware attacks, which technically violate the RFCs. But we think the RFCs will change overtime to accommodate and endorse this kind of optional, opt-in, interception of malicious and harmful traffic…”
Boodah : yes. To prevent, you must configure manually another DNS server instead of your ISP’s one. Some very known examples are Google’s 8.8.8.8 and 8.8.4.4, it is valid until Google starts hijacking too ;-)
GooD and useful !!
I wanted to thank you for the extensive knowledge. It’s helped me understand what’s going on. Every time I log on to a particular site this 3(NXDOMAIN) is sure to be on within a couple minutes. Thanks again.
Thanks this was really useful! I really like people that do things like this for the good of everyone.
Grammar??
How could you not understand the DNS hijacking? It’s simple…ISP forwards you to an ad page if the domain you are trying to get to is not found.
In the case of Verizon FIOS, they use .12 as the last octet in their DNS servers. They provide an alternate ending in .14 which will not redirect NXDOMAIN. I just learned this in researching a problem I was having. I believe it is directly relevant to this thread. So far it seems to be correct and has solved another issue for me.
Receiving this error message cannot correct. If I have been hijacked how do I fix?
Could anyone explain what it means when I show 2 email addresses for myself in my contact list. The one I’m concerned about has my correct email address but instead of gmail.com it has gmail.comandroid? My gmail has many odd things in it, as does my iPhone. It seems my mail is being forwarded to that address? I only use an iPhone to get my mail. On a side note I can see search history on my iPhone of specific sites that I did not look up. When I took my phone to my provider I was told either I looked it up or someone physically took my phone and looked it up. I have taken screen shots of a lot of strange things. Would be great if someone could explain to me.
I’m no where near an expert on these matters, Monica, but I’ll tell you the same thing I was told a week or so ago; “Go wipe all your stuff and make sure you get clean installs of everything.” Though I’m certain it goes deeper than that.
This depends on what DNS server you’re connected to, right? So at work, a domain that’s not hijacked, could be hijacked at home using your home ISPs DNS server?
I think this is not a NXDomain question. I just checked and gmail.comandroid is not a registered domain name – NXDomain – probably somebody typed ‘android’ in or pasted it by accident. (I do stuff like that all the time.) Ah, in fact, nothing ending in .comandroid exists.
Do you go websurfing to a site to get your gmail (like gmail.com) or do you use the Mail app? big difference. Either way, check your Mail settings in the Settings app (not in Mail itself) and make sure you’re set to your own email – you can send/receive emails you send to yourself and all that works.
Your contacts – that’s a different story. You can delete any that you’re afraid of, or go change them so that they’re correct. Sometimes email programs add a contact for you if you send email to them – trying to be helpful – even if it was the wrong email address. That could have been the problem.
Just wanted to mention keep up the excellent job!| Greetings from California!
NO, its spelling errors
Curious, is your “own resolving caching dns server” a full DNS server, or are you running a local DNS proxy like Acrylic?
what is problem about my net?
I need help
I can send e-mails but I cannot receive.
My domain is Ilustrador.cl and it has an account in (google)
My e-mail is [email protected]
I don’t understand why it doesn’t work.
Can you help me ?
attentively
Ivan